Spec ID: Fingerprinting for the Agentic Web
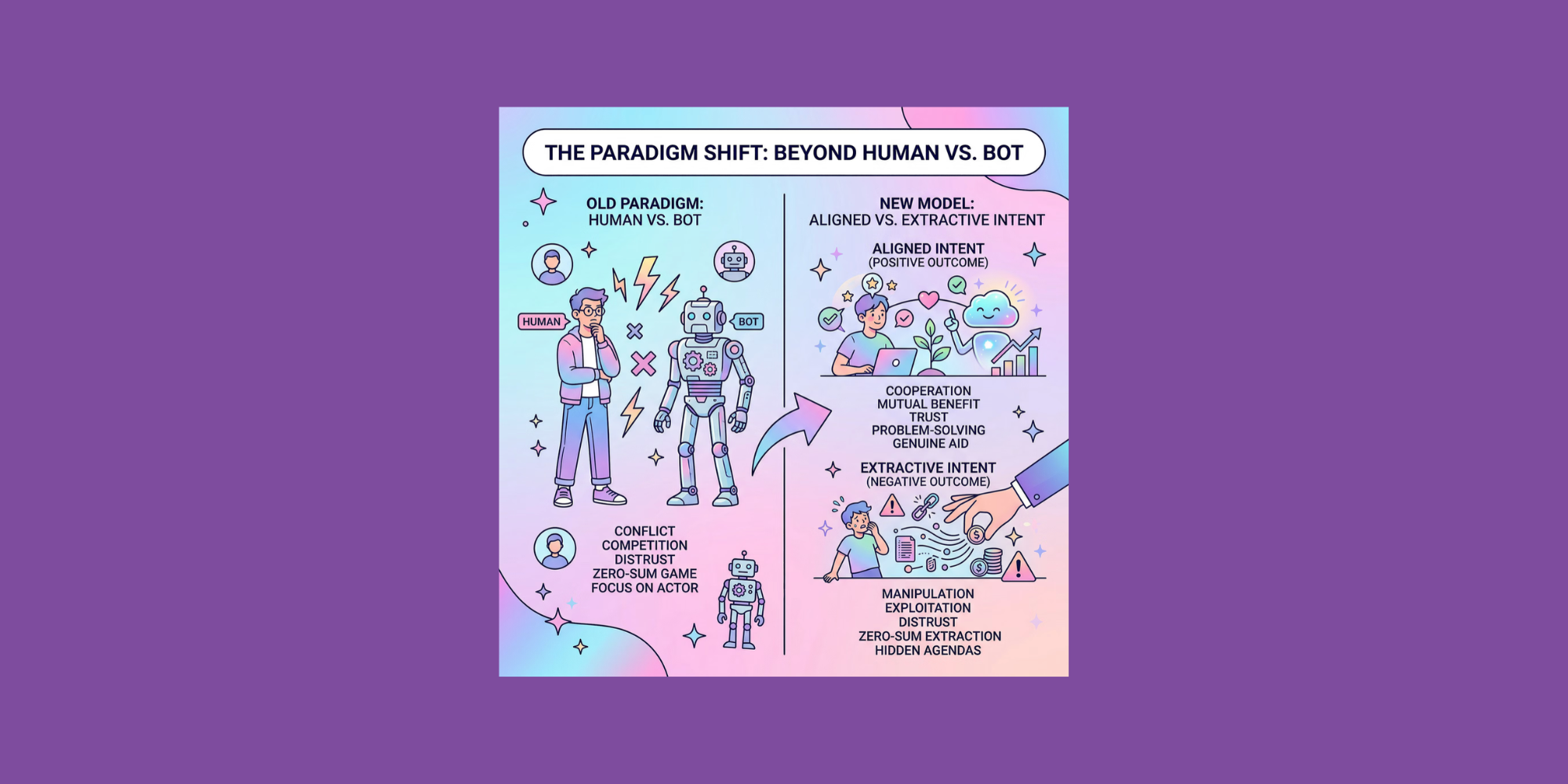
Differentiating legitimate from fraudulent activities in a long list of payments, user logins, or account creations, fundamentally drives the design of modern fraud detection, bot mitigation, and risk systems.
However, attackers rarely operate at the level of isolated events. More frequently, they operate across journeys that span multiple endpoints, sessions, and identities.
They start by exploring the environment:
- Testing login endpoints to determine whether credential stuffing protections exist
- Triggering password reset flows to verify which accounts are valid
- Creating accounts slowly to measure how onboarding defenses respond
- Observing error messages, rate limits, and mitigation triggers
Only after understanding the system do they begin executing the actual attack.
This activity can stretch across hours or days. It might involve different IP addresses, different user agents, and different account identities. In many cases, it spans both logged-out and logged-in experiences.
From the attacker’s perspective, this is a single coordinated effort.
From the perspective of most security teams and systems, it appears as a series of unrelated events.
Why Event-Based Detection Misses Coordination
When detection systems evaluate activity one interaction at a time, they lose visibility into the broader structure of an attack.
Login attempts, password reset requests, or new accounts may appear legitimate based on initial behavior, but the coordination becomes visible when those interactions are connected together.
Without a durable identity layer linking these events, the system can’t see the attacker’s full journey. Each request appears to originate from a new visitor and each action is evaluated without the context of what came before.
Attackers exploit this fragmentation deliberately.
They rotate infrastructure, generate disposable identities, and vary browser signals in order to ensure that detection systems never observe their activity as a single sequence.
The attack remains hidden because the system can’t see how they relate to one another.
The Limits of Device-Based Identity
JavaScript-based device fingerprinting allowed systems to collect attributes from a browser environment and generate a persistent identifier tied to a device. This made it possible to recognize returning users across sessions and correlate behavior over time.
However, it also depended on a critical assumption: the browser environment would cooperate. More explicitly, JavaScript would execute to expose enough information to generate a fingerprint.
In an adversarial environment, that assumption is fragile.
Attackers increasingly manipulate browser signals, emulate legitimate environments, or bypass browser execution entirely through headless automation frameworks. A growing share of internet traffic now originates from automated clients that never execute JavaScript at all.
When the browser doesn’t cooperate, device ID disappears.
When device ID disappears, the system returns to evaluating events in isolation, which creates a structural gap between events and actors.
And without a way to consistently identify the actor behind actions, systems only see fragments.
The reconnaissance phase appears unrelated to the exploitation phase, making simple probing seem unrelated to any actual fraud behind it.
Identity That Persists Across the Journey
To reveal coordination, identity must:
- Connect activity that occurs before authentication, such as browsing behavior and login attempts
- Link behavior that occurs after authentication, including account actions and transactions
- Maintain continuity even when attackers rotate IP addresses, change devices, or manipulate browser signals
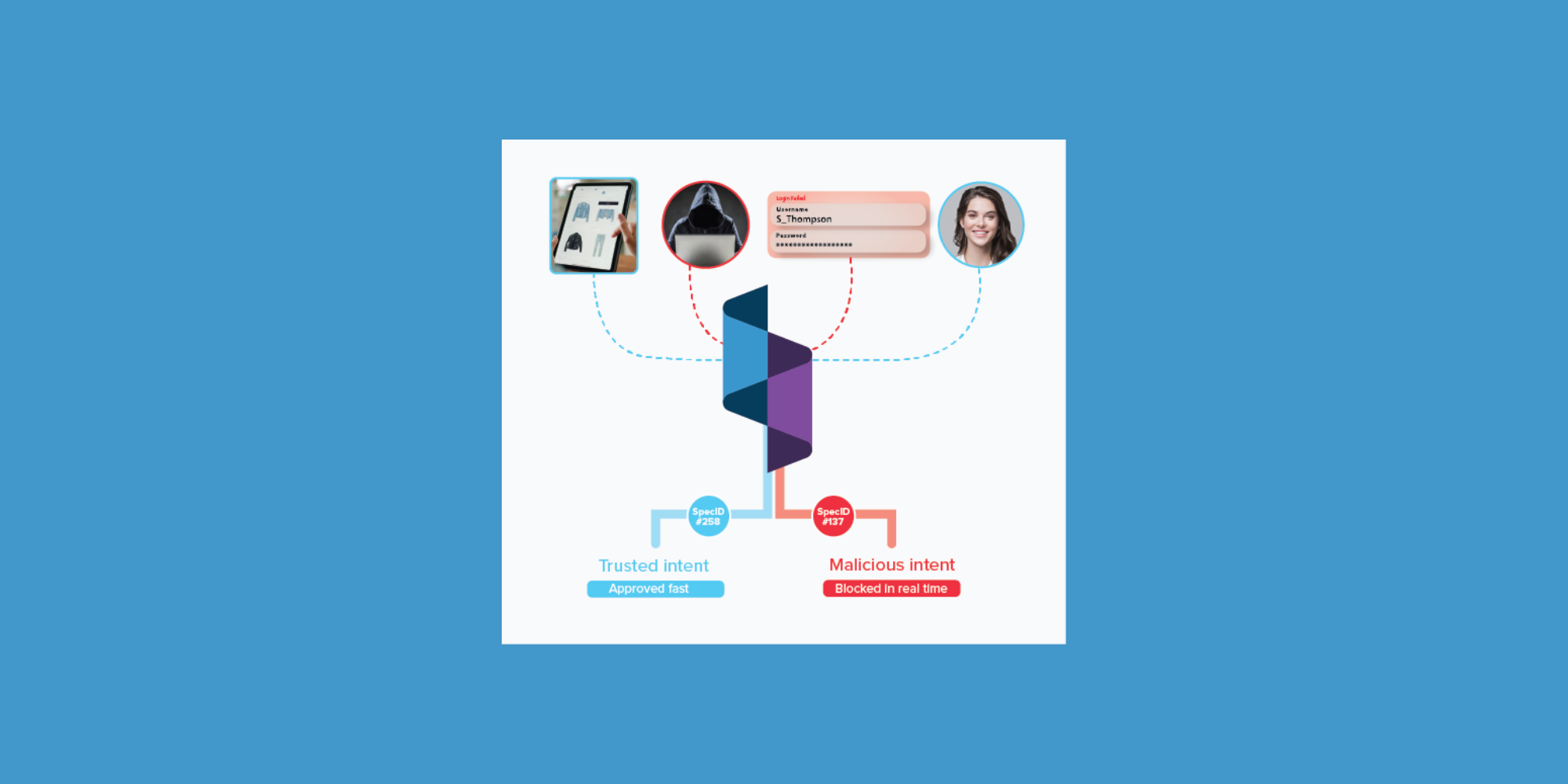
Spec ID provides this continuity.
Instead of relying on client-side instrumentation or browser execution, Spec ID is generated using passive observations at the network layer. By operating independently of the browser environment, it remains available even when JavaScript is blocked, cookies are absent, or automated clients interact through headless frameworks.
Spec ID derives a deterministic identifier from behavioral, temporal, and network-level signals observed across requests. These signals are processed in real time to establish a persistent identity that links interactions across sessions and endpoints.
Because this identity is established outside of the client environment, attackers can’t easily manipulate it by modifying browser behavior or rotating superficial identifiers.
From the first network request onward, activity is tied to a consistent actor.
- Seemingly unrelated interactions begin to connect
- Login attempts are linked to earlier probing behavior
- Suspicious transactions can be traced back to the infrastructure used during reconnaissance
- Signup activity is correlated with broader patterns of promotion abuse or synthetic account creation
What previously appeared as statistical noise becomes a coherent behavioral pattern as thousands of fragmented interactions collapse into a single identity.
Spec ID allows teams to move from reacting to individual events to understanding the structure of an attack.
Spec ID: The Missing Identity Layer
Modern security stacks contain multiple layers of detection, like network protections, fraud scoring models, bot mitigation tools, and identity verification systems – each contributing valuable signals and mitigations.
But without a durable identity layer connecting interactions across the full journey, even sophisticated detection models struggle to identify coordinated activity.
Spec ID fills this gap.
With Spec ID, identity exists at the level of the journey and security systems gain a fundamentally different view of online activity.
This visibility allows organizations to detect coordination earlier, respond more precisely, and automate defenses with greater confidence. Identity becomes an infrastructure layer that strengthens everything built on top of it.
In an environment where attackers deliberately fragment their activity to evade detection, the ability to reconstruct the full journey becomes one of the most valuable capabilities a security platform can provide.
And as the internet becomes increasingly agentic, more interactions will be driven by systems capable of coordinating behavior across infrastructure, time, and identities.
Understanding the actor behind those interactions will become foundational.
Spec ID makes that possible.
Ready to get started with Spec?
Nate Kharrl, CEO and co-founder at Spec, has built leading solutions for application security and fraud challenges since the early days of the cloud era. Drawing from his cyber experience at Akamai, ThreatMetrix, and eBay, Nate helped found Spec to focus on the needs of businesses operating in a landscape of increasing AI risks. Under Nate’s leadership, Spec grew from its mid-pandemic founding to raise $30M in venture-backed funding to build solutions used by Fortune 500 companies transacting billions in online commerce. Spec’s service offerings today include protective measures for websites and APIs that specialize in defending against attacks designed to bypass bot defenses and risk assessment platforms.